David Braue is an award-winning technology journalist who covers the security and telecommunications industry in Australia. The average ransom payment by Australian companies reached $1.3 million during the first five months of 2022, Palo Alto Networks’ Unit 42 security arm recently revealed, representing a 71% increase over last year and triple the average payment in 2020. The theft of sensitive data has become commonplace as cybercriminals continue to expand their strategies for attacking target companies. However, the agency had engaged identity-theft support agency IDCare to look after NDIS members whose identity data had been compromised in the breach—a common step after data breach incidents where personally identifiable information has been compromised. “Although we cannot confirm the details of all the data in the time available to be extra careful we are treating any information held in our database as being compromised including documents containing personal information relating to our customers and their clients and carers,” CTARS said in a statement. The country whose identity details attract the highest price online is Ireland, whose citizens’ identity sets are selling online for an average of $305.52 each.
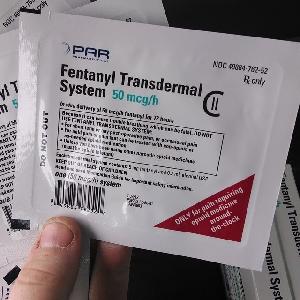
In the obscured recesses of the australian darknet vendors ecosystem, operations are characterized by a high degree of opsec sophistication and regional market specialization. These vendors often leverage the country's geographic isolation and relatively strong domestic postal security to distribute substances like prescription opioids and synthetic drugs with a lower perceived risk of international interdiction. The community is fragmented, with discreet forums and encrypted channels serving as the primary venues for vetting and transaction, creating a closed-loop economy that is notoriously difficult for external actors to penetrate.
- This robust legal trade framework, however, exists alongside a more clandestine digital economy where the nation’s role is less official but increasingly notable.
- However, the agency had engaged identity-theft support agency IDCare to look after NDIS members whose identity data had been compromised in the breach—a common step after data breach incidents where personally identifiable information has been compromised.
- However, if we go into the darknet, we’ll be able to find those same items with very little risk of someone finding out.
- The operation highlighted the growing sophistication of law enforcement in tracking and apprehending those who exploit the anonymity of the darknet.
- Although there has been no confirmation about whether CTARS was also breached by ransomware, the technique has become so effective that many companies are paying increasingly large ransoms to prevent the publication of data and restore business operation.
Substance use across Australia has seen significant discussions and variations over the years, especially with the rise of digital marketplaces operating on the darknet. As authorities continue to adapt to the evolving landscape of drug distribution, it’s crucial to recognize the role that dark web marketplaces play in shaping substance use in Australia. The anonymity provided by these platforms has drawn in users looking for easier access to drugs while avoiding law enforcement. This underground marketplace thrives on anonymity, allowing individuals to acquire drugs without traditional barriers. One such operating system, Whonix, is designed to provide anonymity and security for users venturing into the darknet. The Australian darknet landscape has seen a rise in various vendors offering a range of products, with drug sales being one of the more prominent categories.

Trust within these networks is ephemeral, built painstakingly through escrow systems and verified feedback, yet constantly undermined by exit scams and law enforcement infiltration. The logistical chain is typically streamlined, with domestic shipping preferred to avoid customs scrutiny, making the local consumer market both lucrative and perilous. Vendors often adopt a transient, nomadic digital presence, migrating between marketplaces and communication platforms to evade persistent targeting by agencies, reflecting a continuous adversarial evolution between illicit entrepreneurship and regulatory pursuit.
The digital landscape is complex, and understanding its various layers is crucial for public awareness. One such layer, often shrouded in mystery, involves the online trade of illicit goods. This article aims to inform by examining the operational realities surrounding Australian darknet vendors, providing a clear, factual overview of how these networks function, the associated risks, and the broader implications for online safety.
Australian Darknet Vendors
The term Australian darknet vendors refers to individuals or groups operating within Australia who use encrypted, anonymized networks to sell goods and services. These vendors typically list their products on hidden marketplaces, accessible only through specific software. While the darknet itself is a tool for privacy, its illicit corners are defined by transactions involving narcotics, stolen data, and other illegal commodities.
How These Networks Typically Operate
The ecosystem is built on layers of technology and trust. A vendor's reputation is paramount, often built through a feedback system similar to legitimate e-commerce platforms. The process generally follows a pattern:
- Vendor Onboarding: An individual sets up shop on a marketplace, creating listings with detailed descriptions and prices, often in cryptocurrency.
- Customer Interaction: Buyers browse anonymously, communicating through encrypted messaging systems.
- Transaction & Logistics: Payment is held in escrow by the marketplace until the buyer confirms receipt. Products are then shipped using discreet packaging methods, with Australian darknet vendors relying on domestic postal systems to avoid international customs scrutiny.
- Feedback Loop: Both parties leave reviews, cementing the vendor's reputation for reliability or quality of product.
The Significant Risks and Consequences
Engaging with these markets carries severe dangers, far beyond legal repercussions.
- Law Enforcement Operations: Australian and international agencies continuously monitor these spaces. High-profile police operations have repeatedly shut down markets and identified vendors and buyers.
- Financial Scams: The lack of regulation leads to "exit scams," where marketplace administrators disappear with all the held escrow funds, or vendors simply fail to deliver after payment.
- Physical Danger: Products, especially chemicals or drugs, are unregulated and can be lethally adulterated. There is no quality control or accountability for the substances sold.
- Cybersecurity Threats: Marketplaces are hotbeds for malware. Links, files, and even vendor profiles can be designed to steal a user's cryptocurrency or compromise their anonymity.
Why Public Awareness Matters
Understanding the mechanics of these hidden markets is a critical component of modern digital literacy. It demystifies the process and highlights the very real human and legal costs involved. Knowledge of the tactics used by Australian darknet vendors and the associated risks empowers individuals to make informed decisions, recognize the signs of illegal online activity, and ultimately protect themselves and others from harm.
Frequently Asked Questions (FAQs)
- The collaborative effort spanned multiple countries, dismantling key networks and seizing substantial quantities of drugs, firearms, and illicit proceeds.
- Ausking runs his business based on the philosophy that people should be allowed to choose their own form of recreational drugs since the legal ones such as alcohol and nicotine are just as harmful.
- In March 2015, the Evolution marketplace performed an "exit scam", stealing escrowed bitcoins worth $12 million, half of the ecosystem's listing market share at that time.
- Almost all dark web marketplaces have implemented some sort of review system or trust rating for vendors, making it easy to keep track of which dark web vendors are honest and reliable.
- Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption.
Q: Is it just drugs that are sold by these vendors?
A: No. While narcotics are a major category, these markets also frequently trade in stolen financial data, hacking tools, counterfeit documents, and other illegal digital goods.
Q: How do authorities track down darknet vendors?
A> Methods include undercover operations, forensic analysis of seized packages, blockchain analysis to trace cryptocurrency payments, and exploiting operational security mistakes made by vendors or marketplace administrators.
Q: Does using privacy tools like Tor make me a target?
A: Using Tor for privacy is not illegal. However, law enforcement may focus investigative resources on traffic to known illicit marketplaces. Legal use of privacy tools is protected, but activity on hidden services is not anonymous from determined, sophisticated investigation.