Mixing uses of both these terms has been described as inaccurate, with some commentators recommending the terms be used in distinct fashions. Since ARPANET, the usage of dark net has expanded to include friend-to-friend networks (usually used for file sharing with a peer-to-peer connection) and privacy networks such as Tor. Anonymous communication between whistle-blowers, activists, journalists and news organisations is also facilitated by darknets through use of applications such as SecureDrop. Darren is regularly featured as a cyber-security expert in major media outlets including CBS Evening News, Fox & Friends, USA Today, ABC and Mashable. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC. There are several whistleblower sites, including a dark web version of Wikileaks.
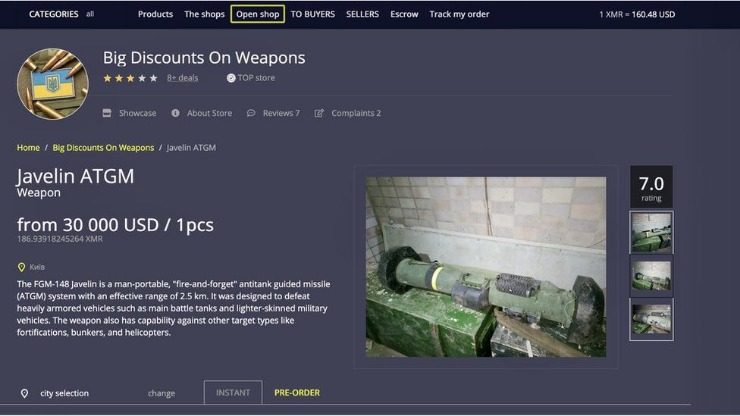
To access darknet markets, one typically employs specialized software like Tor to navigate to .onion URLs, which are not indexed by conventional search engines. These markets operate on encrypted networks, requiring cryptocurrency for transactions to maintain anonymity. They host a range of illicit goods and services, from narcotics to stolen data, exploiting the decentralized and pseudonymous nature of the dark web.
Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic.
To keep a closer eye on your personal information, you can use services like NordStellar's dark web monitoring. In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored. It offers access to hacked bank accounts, credit card data, and cryptocurrency laundering tools. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity. The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots.
Engaging with these platforms carries significant legal and security risks, as law enforcement agencies actively monitor and infiltrate such spaces. Users may expose themselves to malware, scams, or criminal prosecution. The infrastructure is designed to obscure identities, but vulnerabilities exist, and participation often supports illegal activities with real-world consequences.
The digital world extends far beyond the familiar websites indexed by popular search engines. A vast, layered network exists beneath the surface, and within it, a controversial segment known as darknet markets often sparks public curiosity. Understanding this hidden ecosystem is crucial, not to encourage participation, but to demystify its operations, highlight its significant dangers, and ultimately promote informed digital safety.
Access Darknet Markets
Gaining visibility into how individuals access darknet markets is a key step in understanding the broader landscape. It is not as simple as opening a standard browser. This process inherently involves specialized tools and software designed to anonymize user traffic and obscure website locations.
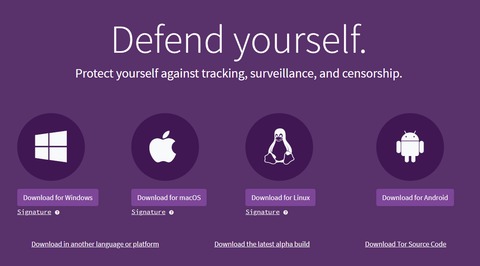
The Gateway: Specialized Software

The primary tool required to access darknet markets is The Onion Router, or Tor Browser. This free, open-source software routes internet traffic through a worldwide, volunteer-run network of servers, encrypting the connection multiple times to conceal a user's location and activity. It allows access to ".onion" websites, which are not reachable through standard browsers like Chrome or Firefox.
Beyond the Browser: Essential Precautions
Even with Tor, users on these networks take extensive, often complex, security measures. These can include:
- A Taiwanese man was sentenced to 30 years in prison for operating Incognito Market, one of the world's largest online narcotics marketplaces that sold over $105 million worth of illegal drugs to customers worldwide.
- By employing best practices, such as using VPNs, recognizing scams, and maintaining digital hygiene, individuals can navigate these markets more safely.
- The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below.
- Quality and validity of the data it provides justify its higher cost over other marketplaces.
- Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services.
- To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
- Virtual Private Networks (VPNs): Used by some in conjunction with Tor for an added layer of obfuscation, though this is a debated practice.
- Cryptocurrencies: Transactions are almost exclusively conducted using cryptocurrencies like Bitcoin or Monero, which offer a degree of financial anonymity compared to traditional payment methods.
- Operational Security (OPSEC): A set of practices that includes using encrypted communication, avoiding personal information reuse, and being highly skeptical of other users.
Navigating and the Reality of Risk
Finding these markets often relies on dynamic directories and forums that are themselves hosted on the darknet. However, the act to access darknet markets is fraught with extreme and immediate risks:
- Legal Consequences: Law enforcement agencies globally monitor these spaces. Participation in illicit trade is a serious crime.
- Scams and Fraud: "Exit scams," where market administrators disappear with users' funds, are common. Products are often misrepresented or never delivered.
- Cybersecurity Threats: Markets are hotbeds for malware, phishing attempts, and hacking aimed at stealing cryptocurrency or personal data.
- Dangerous Substances: Products are unregulated and can be lethal, leading to severe health risks.
Frequently Asked Questions (FAQs)
Is using the Tor Browser illegal?
No, the Tor Browser itself is a legal privacy tool used by journalists, activists, and citizens worldwide to protect their anonymity online. It is the activities conducted with it that may be illegal.
Can you truly browse anonymously?

Anonymity is never absolute. While Tor provides strong privacy protections, sophisticated adversaries and user mistakes can potentially de-anonymize individuals.
Why do darknet markets exist if they are illegal?
They exploit the anonymizing technologies designed for legitimate privacy purposes. Their persistence is a challenge of global jurisdiction and the decentralized nature of the infrastructure.
What should someone do if they are curious about this topic?
Seek information from reputable cybersecurity and digital literacy resources. Understanding the mechanisms and dangers from an educational standpoint is the safest and most responsible approach.