For instance, you can use the Tor browser for regular browsing and private access to deeper parts of the internet. Key reasons to use the dark web legally include stronger privacy, evading censorship, and accessing uncensored news or academic research. Finally, you can check out reputable websites and news outlets like SecureDrop and ProPublica for verified .onion domain addresses. Other alternatives include NotEvil, Ahmia, OnionFind, and Torch, which list .onion links. So, it’s difficult to determine when a popular .onion site is going to disappear or go offline.
It has attracted controversy over the years due to its practice of challenging the current model of academic publishing, but it is a very important resource for researchers from developing countries as well as those who do not have access to universities. Sci-Hub serves as the dark web’s version of a massive online library, giving millions of users free access to legally protected academic papers, books, and scientific resources. The tool is very helpful for researchers, journalists, and security professionals working within the realm of the dark web. While Meta’s own data collection practices are well-documented, accessing their site via Tor ensures that the connection details (your IP address) are hidden from both the ISP and the network itself. This was created primarily for users in countries where the social network is blocked due to government censorship, or for those who simply wish to bypass regional restrictions while accessing the social network. By giving individuals access to the Tor Network, the CIA has been able to demonstrate its confidence in the functionality of the Tor Network’s anonymity as long as it is properly set up.
- Tor is among the best private browsers for anonymous communications and internet freedom.
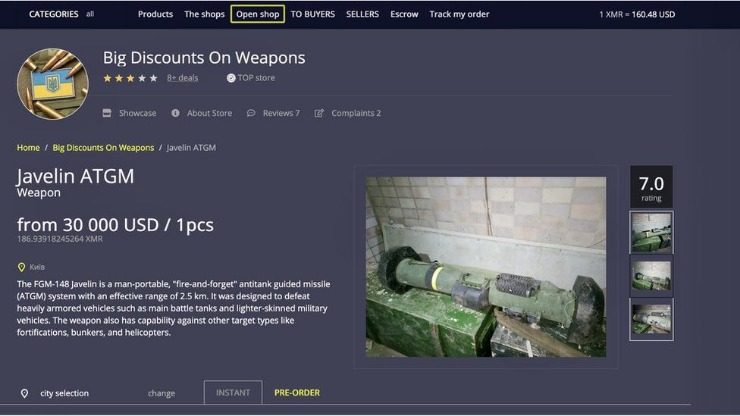
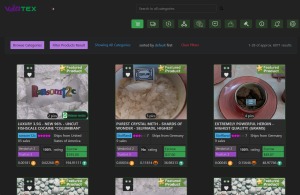
- Dark web marketplaces change frequently because they operate under constant pressure from law enforcement, internal fraud, and technical weaknesses.
- However, we do not recommend using this platform without taking proper precautions, such as anti-malware and a VPN.
- It’s for the good that these sites are not available for the general internet user.
- No fentanyl allowed, which I respect—it’s a mess I’ve seen too many folks get caught up in.
- Telegram’s robust privacy features have inadvertently caused a massive migration of dark web activity, creating a digital Wild West where…
The landscape by 2026 working darknet market would likely be defined by aggressive decentralization and anonymity arms races. Operators would migrate from centralized servers to peer-to-peer or mesh network models, perhaps leveraging temporary storage on unstoppable, encrypted protocols. User access would be mediated through hardened, self-destructing gateway scripts only reachable via specific privacy routing layers, making takedowns nearly impossible as there is no single infrastructure to target.
Markets would integrate privacy-preserving cryptocurrencies by default, possibly using decentralized anonymous escrow services or trustless swap mechanisms to eliminate the central treasury flaw. Advanced reputation systems would be cryptographic and portable, not stored on any market server. This creates a resilient, fragmented ecosystem where the "market" is less a website and more a constantly shifting, self-replicating protocol for illicit exchange, operated by autonomous collectives rather than identifiable individuals.
The digital landscape is constantly shifting, and the hidden corners of the internet are no exception. For researchers, cybersecurity professionals, and policymakers, understanding the operational realities of these spaces is critical for public safety and education. This analysis explores the projected characteristics of a 2026 working darknet market, focusing on the trends and technologies that define its evolution, purely for informational awareness.
2026 Working Darknet Market
By 2026, a functioning darknet market is predicted to be a far cry from its earlier, more rudimentary predecessors. Survival in a high-stakes environment of law enforcement pressure and internal fraud has driven extreme specialization and technological adoption. These platforms are no longer simple online bazaars; they are complex ecosystems built on resilience and anonymity.
Core Characteristics of a Modern Operation
- Since then, local users have had to use bridges to connect to the browser.
- Always conduct your own research or check with certified experts before investing, and be prepared for potential losses.
- The dark web and deep web are home to countless hidden forums where users discuss everything from privacy tools to…
- It allows access to the .onion sites on the dark web that you won’t find using a regular browser.
- The difference with these takedowns versus others is that, typically, shutting down a market means that it is shut down forever.
To remain operational, a 2026 working darknet market would need to integrate several advanced features:
- Decentralized Architecture: Moving away from a single, vulnerable server, future markets will likely operate on decentralized networks or peer-to-peer protocols, making them harder to seize or shut down.
- Privacy-Centric Cryptocurrencies: While Bitcoin may still be used, a greater reliance on privacy coins with enhanced transaction obfuscation features will be standard to complicate financial tracing.
- Advanced Vendor Verification: To combat scams, sophisticated multi-party escrow systems and even pseudo-reputation systems based on cryptographic proofs could replace simple review systems.
- Automated Security: Implementation of automated threat detection for infiltrators, coupled with mandatory use of PGP encryption for all communications, will be baseline requirements.
The Human and Systemic Risks
Despite technological advancements, the fundamental risks associated with these platforms remain severe and are often amplified. Understanding these dangers is the first step in mitigating their impact on individuals and communities.
- Exit Scams Remain Prevalent: The temptation for operators to disappear with users' funds in a "exit scam" is a perpetual threat, regardless of the year or technology.
- Law Enforcement Infiltration: Agencies globally are deploying advanced cyber-investigative techniques, making every user a potential target for identification.
- No Legal Recourse: Users have zero protection. Transactions are illegal, and theft, fraud, or the sale of dangerous products carry no guarantees or avenues for complaint.
- Malware and Phishing: These sites are breeding grounds for digital threats, with links, downloads, and even other vendors designed to steal cryptocurrency or personal data.
Frequently Asked Questions (FAQs)
Q: How do people even find a 2026 working darknet market?
A: Access requires specific anonymizing software and knowledge of constantly changing addresses, often shared in closed, vetted communities. Public searches are unreliable and risky.
Q: Is the darknet only for illegal activities?
A: No. The underlying network provides anonymity for whistleblowers, journalists in oppressive regimes, and legitimate privacy-seeking individuals. However, markets specifically facilitate illegal commerce.
Q: What is the biggest misconception about these markets?
A> That they are safe or anonymous for users. Every interaction carries immense risk of financial loss, legal prosecution, or exposure to serious cybercrime.
Q: Why is it important for the public to be informed about this topic?
A> Awareness demystifies these platforms and highlights their severe dangers. This knowledge can deter curious individuals, help the public recognize related cyber-threats, and foster support for constructive solutions to the underlying societal issues that drive demand.