Based on the results, I asked follow-up questions to gain more insights, and the tool even suggested prompts for expanding the data analysis. Sample box plot from Julius AI showing the distribution of self-reported productivity across work models based on a fictional data set. It also created boxplots and stripplots so I could visualize the distribution of metrics within the dataset.
Navigating the evolving landscape of decentralized commerce in 2026 requires understanding that the term best working darknet market is inherently fluid. It refers not to a static entity but to a temporary convergence of reliability, security features, and vendor reputation. Current discussions suggest that any platform claiming this title would likely operate on a closed-loop, invitation-only model with escrow-less, multi-signature transactions and built-in, delay-forwarding network obfuscation as standard. Market longevity is now measured in months, not years, with the "best" often being the one that has not yet attracted disruptive attention or suffered a catastrophic exit scam.
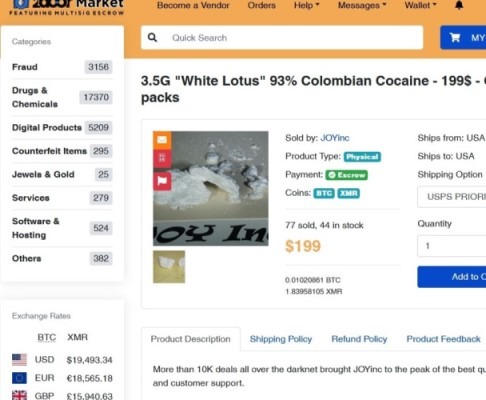
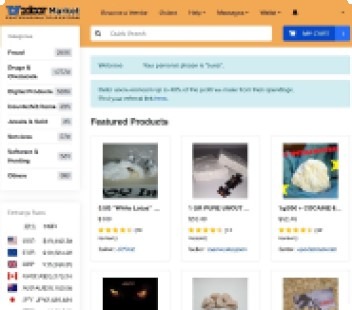
After selecting the desired products and adding them to a cart, the user proceeds to a checkout page where a unique Bitcoin wallet address is generated for the order. The platform's search functionality and vendor rating system reduce the time required to source high-quality products, from common substances to more specialized offerings. This action directly connects them to the market interface, where they can proceed with registration, browsing, and transactions. This methodical approach to sourcing links ensures direct and secure entry to platforms like Nexus, facilitating a seamless transition to browsing and purchasing.
The defining characteristic of a leading market in this period is its post-marketplace architecture. Rather than acting as a centralized repository of goods and listings, the most resilient systems function as automated, decentralized coordination layers for peer-to-peer deals. They provide standardized templates for secure communication and transaction finalization while holding minimal user funds or data directly. This model drastically reduces the attack surface for law enforcement and eliminates the single point of failure that has doomed previous major markets. Success is thus gauged by operational stealth and the robustness of its dispute resolution protocol, rather than by public brand recognition.
These sites use “.onion” domains, which are made up of random letters and numbers up to 56 characters long. Onion sites, or dark web websites, are sites on the dark web that can typically only be accessed using special software like the Tor browser. The Budget emphasises strengthening healthcare services and positioning India as a global destination for medical value tourism. The Union Budget 2026–27 reinforces the role of services as a core driver of growth, employment, and exports, supported by targeted institutional and skills-building interventions. These measures aim to enhance productivity, support value addition, and strengthen India's position in global textile and apparel markets. Radar Rundown The dark web hosts a ton of legal and illegal websites that contain unrestricted infor…
Navigating the digital underground requires understanding its landscape. Discussions about the best working darknet market 2026 often focus on technical resilience, security features, and community trust, rather than any specific illicit purpose. For researchers, cybersecurity professionals, and journalists, analyzing these platforms provides critical insight into evolving encryption, decentralized systems, and the ongoing battle for digital privacy.
Best Working Darknet Market 2026
Predicting the specific leader for 2026 is impossible due to the volatile nature of these ecosystems. Markets frequently exit scam, face law enforcement takedowns, or are outcompeted. However, the platforms that tend to survive and be labeled as "best working" consistently demonstrate a core set of features. These characteristics define operational stability and user confidence within this high-risk environment.
- Escrow services and Chinese-language “guarantee” marketplaces have become a central settlement layer in cross-border laundering, particularly among Chinese money laundering organizations operating across the Asia-Pacific (APAC) region.
- This guide covers the top dark web marketplaces and what they sell.
- Hansa started out as a trusted, well-moderated market with vendor vetting, escrow, and a diversified product selection.
- Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts.
- SearX is a privacy-focused metasearch engine accessible on both the clear web and the dark web.
Core Features of a Resilient Platform
Any platform that remains operational over time typically invests heavily in several key areas:
- Advanced Security Protocols: Mandatory use of PGP encryption for communication, robust two-factor authentication (2FA), and a clear commitment to protecting user anonymity through Tor and beyond.
- Escrow and Dispute Resolution: A secure escrow system that holds funds until the buyer confirms receipt, coupled with a fair and transparent mediation process handled by impartial staff.
- Decentralized Infrastructure: A move away from centralized servers to decentralized or peer-to-peer architectures, making the platform more resistant to single-point takedowns.
- Community Reputation and Transparency: Active community forums with verifiable feedback mechanisms. Long-standing vendor histories and clear, consistent operational rules build essential trust.
Understanding the Constant Evolution
The landscape is in perpetual flux. A market hailed as reliable today could vanish tomorrow. This cycle is driven by several factors:

- Law Enforcement Pressure: Global operations like "SpecTor" or "Dark HunTor" demonstrate ongoing, sophisticated campaigns targeting market infrastructure.
- Internal Exit Scams: Operators may suddenly shut down, absconding with all the funds held in user and vendor escrow accounts, a constant risk in an anonymous setting.
- Technological Arms Race: As security improves for users, so do forensic techniques. The best working darknet market 2026 will need to constantly innovate to stay ahead.
Frequently Asked Questions (FAQs)
Q: Is it safe to access these markets for research?
A: Accessing these sites carries inherent risk. Even with Tor and security tools, researchers must use dedicated hardware, virtual machines, and extreme caution to avoid malware, phishing, and legal exposure.
Q: What's the biggest misconception about darknet markets?
A: That they are solely for illegal goods. They also function as hubs for whistleblowers, journalists in censored regions, and individuals seeking digital privacy tools, highlighting the dual-use nature of the technology.
- This deprived criminal users of a trusted venue, locked customer balances, and forced displacement into less familiar and potentially more observable channels.
- That said, the social network’s data collection and tracking practices may seem at odds with many of the principles motivating dark web users.
- The platform utilizes end-to-end encryption, ensuring it does not store any activity records.
- The dark net is full of notorious hackers, scammers, malware, and other viruses.
- Instead of admin-held escrow, some dark websites are now using blockchain-enforced smart contracts (e.g., Monero + Particle).
- Across recent years, the largest share of volume routes through VASPs and other service infrastructure, illustrating how illicit actors depend on intermediaries.
Q: Why do markets constantly change their addresses?
A> They use rotating ".onion" URLs to mitigate DDoS attacks and increase operational security. Users must find verified links from reputable, independent directories to avoid phishing sites.
Ultimately, the discussion around the best working darknet market 2026 is less about naming a single platform and more about understanding the principles of operational security, trust, and resilience in anonymous networks. This knowledge is vital for cybersecurity defense, academic study, and fostering informed public discourse on digital rights and privacy.