Identities and locations of darknet users stay anonymous and cannot be tracked due to the layered encryption system. The dark web is the World Wide Web content that exists on darknets (overlay networks) that use the Internet, but require specific software, configurations, or authorization to access. Invest in continuous penetration testing services and security hygiene to close gaps before attackers exploit them.
Accessing the best fraud market darknet requires navigating through encrypted networks using specific software and protocols. These platforms operate as centralized hubs for stolen data, financial malware, and fraudulent services, often featuring vendor rating systems and escrow to facilitate illicit transactions. Their infrastructure is deliberately unstable, with markets frequently disappearing in exit scams or being dismantled by law enforcement operations.
The ecosystem is inherently predatory, targeting both the financial systems and the individuals whose data is commodified. Success in this realm demands significant technical knowledge to avoid scams from other criminals and to evade detection. The pursuit of such a market carries extreme legal risk and contributes directly to widespread financial harm and loss.
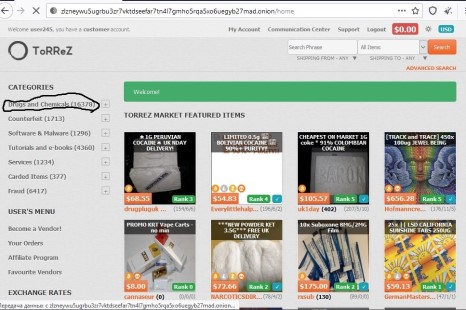
This data then circulates on dark web markets and forums. Full database dumps from breached companies appear on dark web markets and forums. TorZon emerged as a major darknet marketplace in 2025, absorbing vendors displaced from Abacus and other collapsed markets. Security teams monitor these marketplaces to detect exposed corporate data before attackers use it. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. Abacus Market offers an extensive array of illegal goods and services across various categories, making it one of the most versatile marketplaces on the dark web.
The digital underground is a complex and shadowy ecosystem, often misunderstood by the general public. While its existence is frequently sensationalized, understanding its mechanics is a critical component of modern cybersecurity literacy. This examination focuses on the mechanisms behind illicit platforms, specifically to educate on how they operate and the profound risks they pose, thereby empowering individuals with knowledge that can safeguard their financial and personal security.
Best Fraud Market Darknet
When discussing the concept of a best fraud market darknet, it is crucial to frame it not as a recommendation but as an analysis of common features that define these illicit hubs. These platforms operate on hidden networks, requiring specific software to access. They function as anonymous marketplaces where stolen data and fraudulent services are commoditized, posing a severe threat to global economies and individual privacy.
Common Features of High-Traffic Fraud Platforms
Despite their illegal nature, these markets often mimic legitimate e-commerce sites to build user trust. Key characteristics include:
- Almost all dark web forum activities are illegal, and hence, the last thing users want is to reveal their real identities.
- Operating on both the dark web and the surface web, Exploit.in serves as a hub for malicious actors seeking to buy and sell exploits, malware, and stolen data.
- Despite how big the dark web forum market is, or how many people it attracts, these forums remain a risk to both individual users and businesses.
- Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see.
- Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn't foolproof.
- Escrow Services: Temporary holding of funds until a transaction is completed, though exit scams are rampant.
- Vendor Feedback Systems: Reputation scores and reviews, which are often manipulated or fake.
- Anonymized Communication: Built-in encrypted messaging systems for buyers and sellers.
- Diverse Product Listings: These can range from stolen credit card details (dumps) to full identity packages and malware.
The Real-World Impact and Dangers
Engaging with or being affected by these markets has severe consequences. For the end-user whose data is sold, the result can be financial ruin, damaged credit, and a lengthy recovery process. For those curious about accessing them, the risks are multifaceted:
- Legal Repercussion: Law enforcement agencies actively monitor these spaces, leading to prosecution.
- Malware and Scams: Downloading files or links often results in infection, turning the visitor into a victim.
- No Consumer Protection: Transactions are final, and there is no authority to appeal to in case of fraud.
Protective Measures for Individuals and Businesses
Awareness is the first line of defense. To protect against the threats originating from these sources:
- Use strong, unique passwords and enable multi-factor authentication on all accounts.
- Monitor financial statements and credit reports regularly for unauthorized activity.
- Educate employees and family members on phishing tactics, a primary source of stolen data.
- Keep all software updated to patch security vulnerabilities.
Frequently Asked Questions (FAQs)
Q: Are these markets easy for anyone to find and access?
A: While they exist on hidden networks, they are not indexed by traditional search engines. Finding them requires specific technical knowledge, but this barrier is not absolute.
Q: Why is it important for the public to know about these markets?
A> Informed awareness demystifies the threat. Understanding that your personal data is a commodity on these platforms reinforces the importance of rigorous personal cybersecurity hygiene.
Q: Can law enforcement actually shut down these operations?
A> Yes, international law enforcement collaborations have successfully taken down major platforms through operations like "Darknet Takedown Days." However, the hydra-like nature of the darknet often sees new sites quickly emerge.