Accessing the dark web typically requires specialized software, most commonly the Tor network, which anonymizes a user's connection by routing it through a series of volunteer relays. This process obscures the original IP address, allowing one to reach hidden services with addresses ending in .onion that are not indexed by standard search engines. The intent is to provide privacy and circumvent censorship, though the environment also hosts illicit marketplaces and forums.
The deep web simply encompasses everything that sits behind a login, paywall or other access control—corporate intranets, streaming queues, medical records, even your private Google Docs. The terms “deep web” and “dark web” often appear interchangeably in headlines, but they describe very different slices of online reality. Roughly 12,600 volunteer relays power the network as of April 2025, keeping any single observer from tracing both sender and recipient.
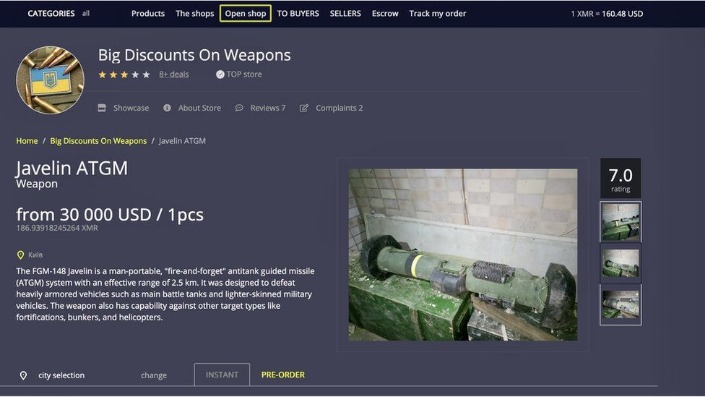
Navigating this space carries significant risk, including exposure to malicious software, scams, and illegal content. Law enforcement agencies actively monitor certain dark web corridors, and unwary visitors can easily compromise their anonymity through simple mistakes. While it houses legitimate tools for whistleblowers and journalists, the dark web's reputation is primarily shaped by its unregulated black markets and criminal enterprises operating in the shadows of the internet.
- Dark web monitoring tools are similar to a search engine (like Google) for the dark web.
- Moreover, the dark web is rife with cybersecurity threats.
- For this tutorial, I’ve used Universal.
- Built in 2019 by anonymous activists, Excavator would be an extremely deep digger into the onion content, trying to be open for everything.
- It’s a good idea to connect to a trusted VPN before you even open the Tor Browser to access the dark web.
- It's something built into the password management services offered by Apple and Google as well, so you don't need to trawl through data leaks manually yourself.
The internet is a vast landscape, but what we see daily is just the surface. Beneath it lies a deeper layer known as the dark web, a part of the internet not indexed by traditional search engines. Understanding accessing the dark web is crucial for digital literacy, as it demystifies a complex topic often shrouded in misconception. This knowledge empowers individuals to comprehend the full architecture of the online world and the importance of cybersecurity.
Accessing The Dark Web
Contrary to popular belief, the dark web itself is not inherently illegal. It is a collection of websites that require specific software and configurations to visit. The most common tool for accessing the dark web is the Tor Browser. This browser anonymizes your connection by routing it through a global network of volunteer-run servers, encrypting the data multiple times. This process helps protect users' privacy and location.
Why Do People Access the Dark Web?
The motivations for visiting this hidden network are diverse. It serves as a vital tool for privacy advocates, journalists communicating with whistleblowers, and citizens in oppressive regimes seeking uncensored information. However, its anonymity also attracts illicit marketplaces. This duality is precisely why public awareness is essential.
Essential Precautions and Steps
If researching this topic for educational purposes, extreme caution is paramount. The environment carries significant risks.
- Use Dedicated Security Software: Ensure your device has robust, updated antivirus and firewall protection before considering any access.
- Download Tor Browser Safely: Only download the Tor Browser from its official, verified website to avoid malicious copies.
- Never Disable Security Settings: The Tor Browser comes with strict security levels. Do not disable these for any website.
- Guard Personal Information Relentlessly: Assume every interaction is monitored. Never use real names, email addresses, or any identifiable details.
- Do Not Download Files: Downloading any content from dark web sites is highly risky and can expose your system to malware.
- To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
- Adopt a skeptic’s mindset—question every download, every prompt and every request for information—and you’ll shrink the attack surface that criminals and investigators alike rely on to unmask careless users.
- Insights like these help researchers and advocates understand how and why Tor is being used.
- Then, use the Hidden Wiki or a dark web search engine like Torch or Ahmia to help find onion sites.
- However, stepping into this part of the internet without preparation can expose you to risks.
Common Misconceptions
Many believe accessing the dark web is synonymous with illegal activity. While illegal markets exist, the technology's core purpose is privacy protection. Another myth is that it's a hacker playground; in reality, it requires no special hacking skills to use the Tor Browser, just like any other application.
FAQs About Accessing the Dark Web
Is it illegal to simply browse the dark web?
In most countries, using Tor or browsing the dark web is not illegal. However, engaging in illegal activities on it is against the law, just as it is on the surface web.
Can I be tracked on the dark web?
While Tor provides strong anonymity, it is not 100% foolproof. Advanced techniques, user mistakes (like enabling scripts or sharing personal info), or compromised exit nodes can potentially de-anonymize users.
Do I need a special internet connection?
No. You can download and use the Tor Browser on a standard internet connection. However, some networks or countries may block or monitor its use.
What should I absolutely avoid doing?
Avoid illegal marketplaces, discussions involving illicit activities, downloading files, and clicking on unknown links. Treat every site with extreme suspicion.
Understanding the mechanisms and risks of accessing the dark web is a critical component of modern digital education. This knowledge does not encourage its use for malicious purposes but rather illuminates a hidden part of our digital ecosystem, enabling informed discussions about privacy, security, and the ethical dimensions of online spaces.