Looking for the so-called best dark web sites 2026 is a pursuit defined by volatility and risk. By 2026, the landscape will have evolved far beyond basic marketplaces, likely fragmenting into highly specialized, ephemeral portals. Expect platforms leveraging advanced privacy coins and decentralized hosting to offer not just goods, but controversial data-sets, restricted AI tools, and access to niche expert networks operating in legal gray zones across various jurisdictions.
Any onion websites you visit from these search engines is another story. The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security. Privacy-focused internet users who access onion sites may see greater anonymity while browsing or sharing sensitive information. However, make sure you’re careful which links you click on — some of them lead to sites that contain illegal content and services.
But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.
Success in this environment hinges on real-time community vetting through encrypted channels, as any publicly listed "best" site is inherently compromised. The true destinations will be peer-shared, require multi-signature access, and likely utilize zero-knowledge proofs for authentication. Ultimately, the "best" are those that remain operational and unmentioned, with their reputations built on silent reliability rather than public fanfare.
The digital landscape is constantly evolving, and with it, the layers beneath the surface web grow more complex. Understanding these hidden spaces is a critical component of modern digital literacy. For researchers, journalists, and cybersecurity professionals, knowledge of these networks is a tool for understanding privacy, surveillance, and the flow of information in the 21st century. This overview examines the types of platforms that constitute the best dark web sites 2026, focusing on their stated purposes and the broader ecosystem, always from an educational perspective on infrastructure and anonymity technology.
Best Dark Web Sites 2026
When discussing the best dark web sites 2026, the term "best" often refers to those with the highest reliability, security, and specific utility within their niche. It is crucial to note that these platforms are accessed via specialized software like Tor, which anonymizes traffic. The following categories represent the primary types of services found, analyzed for their operational role within the hidden web.
Privacy-Centric Communication Platforms
At the forefront are secure communication hubs. These sites offer encrypted email, messaging forums, and whistleblower drop systems. They are designed for individuals operating in high-risk environments, such as activists under oppressive regimes or journalists communicating with confidential sources. The best dark web sites 2026 in this category prioritize open-source code, strong end-to-end encryption, and a proven commitment to not logging user data. Understanding their architecture is key to comprehending modern secure information exchange.
Research and Library Archives
- This is where dark web monitoring and threat intelligence become important.
- The biggest and most frustrating part about dark websites is that they live for a short span of time.
- Finally, I found it very convenient you can use TorrentGalaxy without logging in or creating an account, making it accessible for quick, anonymous access.
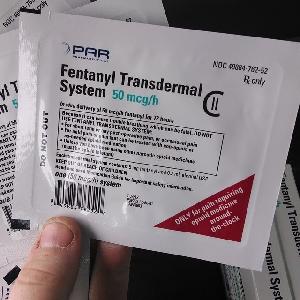
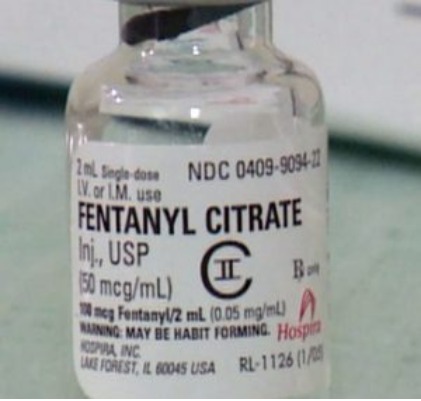
- The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.
- In 2026, good animation supports storytelling.
A significant portion of the dark web is dedicated to the preservation of knowledge and information freedom. This includes vast digital libraries hosting academic papers, books, and historical documents that may be censored, paywalled, or out of print in certain regions. For scholars and students, these archives represent a invaluable resource. The stability and breadth of collections are what define the leading sites in this educational category for best dark web sites 2026.
- The US Navy’s main reason for creating Tor was to help informants relay information safely over the internet.
- With tools like V4 – Transform & Transitions, creators can design purposeful hover states and movement.
- You can access encrypted email services through the onion site without getting tracked.
- In 2026, great designers still follow the same playbook.
- Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
Security and Software Resources
This category is pivotal for cybersecurity education. Reputable sites provide forums for detailed discussions on software vulnerabilities, privacy tools, and anonymity techniques. They often host mirrors for essential privacy software and detailed guides on digital security hygiene. For IT professionals and privacy-conscious individuals, these resources are critical for understanding and mitigating online threats. The most reliable sites are those that foster legitimate, technical discourse and distribute vetted, open-source tools.
Market Dynamics and Platform Longevity
It is an acknowledged fact that commercial marketplaces exist. From an analytical standpoint, studying their lifecycle—how they emerge, guarantee transactions, handle disputes, and ultimately exit—provides profound insights into cryptoeconomics and trust models in anonymous environments. The best dark web sites 2026 that are marketplaces are often characterized by robust feedback systems and escrow services, though their inherent instability is a core topic of study.
Essential Security Precautions and Ethical Considerations
Any exploration of this nature must be accompanied by severe warnings. Accessing these networks requires stringent security measures: using a dedicated operating system, ensuring all software is updated, and employing comprehensive personal opsec. More importantly, the ethical line is clear. This information serves to educate on the realities of network privacy and should empower individuals to protect their data. Engaging with any illegal content is unequivocally dangerous and harmful. True expertise lies in understanding the mechanisms of privacy and security to foster a safer internet for all.