The digital underground operates on a principle of constant flux. When discussing the so-called best darknet market sites, the primary metric is not merely product variety, but resilience and operational security. A market's reputation is built on its escrow system, its forum's community feedback, and the proven integrity of its administrators. Longevity is rare, and a site's prominence is often a fleeting advantage before law enforcement scrutiny or exit scams precipitate its downfall.
This paper described "darknet" more generally as any type of parallel network that is encrypted or requires a specific protocol to allow a user to connect to it. Darknet addresses could receive data from ARPANET but did not appear in the network lists and would not answer pings or other inquiries. "Darknet" was coined in the 1970s to designate networks isolated from ARPANET (the government-founded military/academical network which evolved into the Internet), for security purposes. Mixing uses of both these terms has been described as inaccurate, with some commentators recommending the terms be used in distinct fashions. Additionally, the term is often inaccurately used interchangeably with the deep web because of Tor's history as a platform that could not be search-indexed.
In fact, Tor usage remains high in 2023 the dark web averaged about 2.7 million daily users, with Germany overtaking the U.S. as the country with the most Tor users. KEY TAKEAWAYS If you’re in a hurry, here’s a quick list of darknet search engines of 2026 list… It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. Using TAILS is yet another security measure that protects your online identity on the dark web.
Navigating this landscape requires rigorous operational security beyond just accessing the network. The best darknet market sites are those that have, for a time, successfully balanced visibility with security, implementing features like multi-signature transactions and decentralized hosting. However, any recommended name becomes obsolete quickly; the ecosystem is defined by its chaotic churn. Trust is perpetually provisional, and the notion of a permanent "best" site is fundamentally at odds with the environment's nature.
Between December 28, 2025 and January 16, 2026, Iran’s total crypto volume declined by roughly 60% year over year, while transaction counts fell by approximately 63% compared to the same period in 2024–2025. Even with network disruptions, heightened sanctions pressure, and active conflict, Iran’s crypto rails continued to function as a reliable channel for moving value when traditional financial pathways were most constrained. During the conflict window, Iran’s crypto volume increased by approximately 35%, while transaction counts declined by roughly 40%. The 12-day Iran-Israel conflict from June 13 to June 24, 2025 served as a stress test of Iran’s crypto ecosystem, and highlighted its resilience under acute geopolitical pressure. While activity declined modestly year over year, the scale and consistency of these volumes point to structural demand, not speculative participation. Iran’s crypto economy largely sustained its engagement across 2024 and 2025, showing how deeply digital assets are now embedded in the country’s financial system.
The digital landscape is vast, extending far beyond the familiar websites indexed by common search engines. Beneath the surface lies a part of the internet known for its anonymity and privacy-centric design. Understanding this ecosystem is crucial for digital literacy, as awareness of its structure and risks is a key component of modern cybersecurity knowledge for informed individuals.
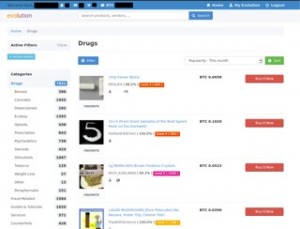
Best Darknet Market Sites
When discussing the concept of the best darknet market sites, it is essential to frame this within a context of understanding how such platforms operate, why they pose significant dangers, and what the legitimate alternatives are for privacy-conscious users. This information serves an educational purpose, highlighting critical risks to avoid.
Understanding the Ecosystem and Its Inherent Risks
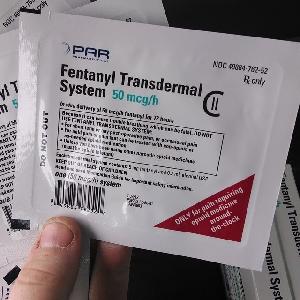
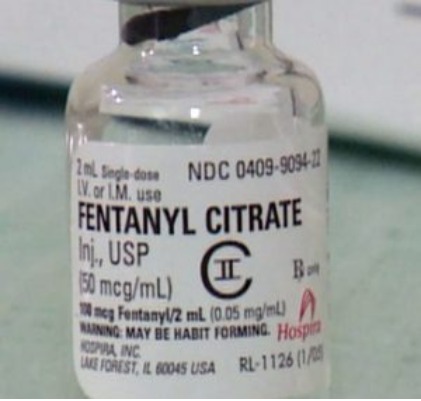
Markets operating on encrypted networks are notoriously volatile and hazardous. They are often associated with illegal goods and services, making them prime targets for law enforcement operations. The so-called best darknet market sites frequently disappear overnight in exit scams, where administrators shut down the site and abscond with users' funds. Furthermore, users expose themselves to severe legal repercussions, malware, and fraud.
Key Characteristics of High-Risk Platforms
- A research study undertaken by Jean-Loup Richet, a research fellow at ESSEC, and carried out with the United Nations Office on Drugs and Crime, highlighted new trends in the use of bitcoin tumblers for money laundering purposes, using escrows.
- Stablecoins were central to Russian sanctions evasion activity in 2025, as they were in other heavily restricted economies.
- With 25,000+ users and 3,000+ vendors, it’s the gold standard for escrow security and scale.
- Researchers often cite Abacus for its rigorous vendor verification processes and consistent uptime, positioning it as a benchmark for trust and stability in darknet market studies.
- “They show an affluent lifestyle with expensive apartments, luxury brands, but with a touch of illicit intrigue.” Many of Telegram’s Russian drug bloggers are most likely sponsored by new darknet drug shops.
Historically, platforms described by some as top-tier shared common traits before their inevitable shutdowns. These included escrow services, user rating systems for vendors, and community forums. However, these features provided a false sense of security. The fundamental nature of these environments means there is no consumer protection, no guarantee of product safety, and no recourse in case of theft.
The Critical Importance of Digital Privacy Tools
For researchers, journalists, and citizens in oppressive regimes, the core technology behind access to these networks—The Onion Router (Tor)—is a vital tool for free communication and information gathering. Legitimate uses for privacy-enhancing technologies include protecting one's identity from mass surveillance, bypassing censorship, and securing sensitive communications. Focusing on these legal and ethical applications is where the discussion of privacy technology should center.
Safe and Legal Alternatives for Privacy
Individuals seeking enhanced online privacy should investigate reputable virtual private networks (VPNs), end-to-end encrypted messaging apps, and secure open-source software. These tools provide substantial protection for legitimate activities without venturing into legally ambiguous or outright dangerous territories. Education on strong password hygiene, two-factor authentication, and recognizing phishing attempts is far more valuable for personal security.
In conclusion, while the terminology of the best darknet market sites circulates in certain online circles, the reality is one of extreme risk and illegality. Informed digital citizens understand that true security comes from using privacy technologies responsibly and within legal frameworks, not from engaging with black markets. This knowledge empowers people to navigate the internet safely and protect their personal data effectively.