To access dark web hidden services, one typically uses specialized software like Tor, which routes traffic through multiple encrypted layers to anonymize the user’s location and activity. This process involves downloading the Tor browser, connecting to the network, and then navigating to .onion addresses, which are not indexed by standard search engines.
Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. Steer clear of forums, marketplaces, or content with illegal intentions.
It’s extremely rare and only useful in very specific cases, like if your VPN is only accessible through Tor. This method sends your VPN connection through the Tor network. Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it.
Once connected, users can find a range of sites, from legitimate privacy-focused forums and whistleblower platforms to illicit marketplaces. It is crucial to maintain operational security, as the environment contains significant risks from malicious actors and law enforcement monitoring. Technical knowledge and caution are essential to navigate these spaces while minimizing exposure to threats.
The internet most people experience daily is just the surface. Beneath it lies a vast, unindexed space often misunderstood and shrouded in mystery. Understanding this hidden layer is crucial for digital literacy, as it highlights both the importance of privacy and the realities of cyber threats. This guide explains its mechanics for educational purposes, empowering readers with knowledge that underscores the value of secure online practices.

The DWSN works a like a regular social networking site where members can have customizable pages, have friends, like posts, and blog in forums. Europol said several pedophile chat sites were also taken down in the German-led intelligence operation. Four people had been detained in raids, including a man from Paraguay, on suspicion of running the network. Scott Dueweke the president and founder of Zebryx Consulting states that Russian electronic currency such as WebMoney and Perfect Money are behind the majority of the illegal actions.
Access Dark Web
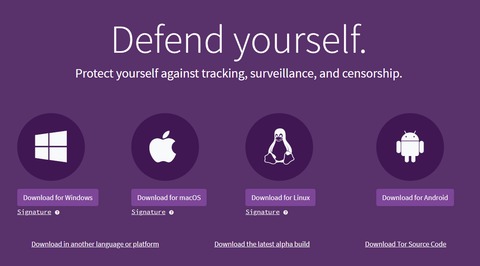
To access the dark web, you cannot use standard browsers like Chrome or Firefox. This part of the internet requires specific software and a mindful approach to security. The most common gateway is the Tor network, designed for anonymity by routing your connection through multiple encrypted layers.
Understanding the Tools: Tor Browser
The primary tool to access the dark web is the Tor Browser. It is a modified version of Firefox that automatically routes your traffic through the Tor network, concealing your IP address. Downloading it from the official Tor Project website is the only safe and recommended method. Using Tor is legal in most countries and is a vital tool for journalists, activists, and individuals seeking privacy from surveillance.
- Facebook’s onion mirror allows people to access it in countries that block the platform, allowing people to connect across digital borders.
- Ahmia also discourages access to illegal content and promotes safer internet practices.
- Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).
- Though the intention and purpose of users on the dark web may vary, the dark web itself is neither good nor bad.
- Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor.
Essential Security Precautions
- However, there are plenty of legal and legitimate online activities that require privacy and anonymity.
- Some content and services on the deep web are indexed by search engines, but paywalls or password protection prevent access.
- It would be problematic if someone could open your private email chains through a simple Google search.
- Also there is no search engine in dark web.
- Review the info and hit Create when you’re done.
Before proceeding, security is paramount. Your mindset must shift from convenience to caution. Never use personal information or real names. Consider disabling JavaScript within Tor's security settings for enhanced protection, though this may break some sites. Crucially, the dark web contains illegal marketplaces and hazardous material; navigating it for education requires discipline and a clear purpose to avoid these areas.
Navigating the Hidden Space

Standard search engines are useless here. You will need to find directories and wikis that list ".onion" links—the unique, scrambled URLs of dark web sites. These resources are often shared on clearnet forums dedicated to privacy. Browsing is significantly slower due to the encryption relays, and sites frequently appear and disappear. Patience and a healthy skepticism are required.
The Critical Importance of Knowledge
Learning how one might access the dark web demystifies its operation and reinforces essential lessons in cybersecurity. It reveals the dual-use nature of privacy technology: a shield for the vulnerable and a tool for criminals. This knowledge empowers individuals to better protect their data, understand the limits of online anonymity, and recognize the architecture of the modern internet. Being informed is the first line of defense in a digital world.