To acess the dark web, one typically employs specialized software designed to route traffic through layered encryption. The most common gateway is the Tor network, which anonymizes a user's connection by bouncing it through a global series of volunteer-run servers, obscuring the original IP address. This provides access to websites with .onion addresses, which are not indexed by conventional search engines and exist on this separate, anonymized layer of the internet.
However, because it's almost completely anonymous, there are a lot of illegal images, information, products, and services on the dark web. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. Take a look at the sites that these directories have collected and see what topics interest you. Do not explore random links to websites you aren't aware of or familiar with.
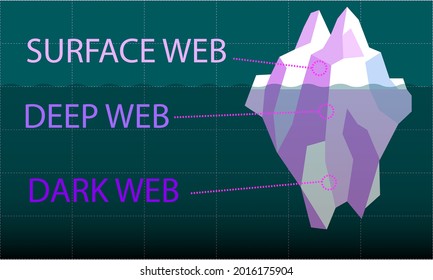
The deep web is crucial for maintaining privacy and security online, as it keeps sensitive information away from the prying eyes of the public and search engines. It includes all the websites and pages that are indexed by search engines like Google, Bing and Yahoo. Remember, while the dark web hosts a range of content, accessing illegal materials or services is, well, illegal. Unlike the surface web, which consists of websites indexed by search engines, dark web websites are not searchable through standard browsers. Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them.
- Tor encrypts your traffic and routes it through multiple volunteer-operated relays, making it difficult to trace.
- The same goes for private networks belonging to companies and other entities.
- On the dark web, traffic is routed through multiple server nodes that don’t log activity, obscuring the user’s origin and enabling anonymous communication.
- Note that your ISP will be able to see you’re connected to Tor.
- Secondly, there are many malicious, fake, and phishing sites on the dark web, which might look like sites you trust but are actually designed to steal your data.
- Unlike the surface web, which consists of websites indexed by search engines, dark web websites are not searchable through standard browsers.
You don’t need special tools or a dark net browser to access most of the deep web; you just need to know where to look. I highly recommend employing another layer of security via a VPN. Another vital precaution is to ensure that your .onion URLs are correct.
The environment contains both legitimate privacy-focused resources and illicit marketplaces. The act of accessing itself is generally legal in many jurisdictions, but navigation carries significant risk. Users encounter severe threats from malware, surveillance by authorities, and criminal elements. It requires rigorous operational security, as the anonymity provided is not absolute and can be compromised by poor user practices or advanced forensic techniques.
The internet is a vast landscape, but what we see daily—social media, news sites, online stores—is just the surface. Beneath lies the deep web, private databases and pages not indexed by search engines. And within that, a smaller, more concealed layer exists: the dark web. Understanding how to acess the dark web is not an endorsement of its illicit corners, but a crucial step in digital literacy. In an age where privacy is paramount and cyber threats are common, being informed about this hidden ecosystem empowers you to understand modern cybersecurity, protect your data, and grasp the full reality of the online world.
Acess The Dark Web
To acess the dark web, you cannot use a standard browser like Chrome or Firefox. This part of the internet operates on overlay networks that require specific software and configurations to provide anonymity. The most well-known tool for this is the Tor network.
Essential Tools and Precautions
Before considering access, the right tools and a mindset focused on security are non-negotiable.
- The Tor Browser: This is the primary gateway. It routes your connection through multiple encrypted layers (or nodes) around the world, obscuring your IP address and location.
- A VPN (Virtual Private Network): While Tor provides anonymity, using a reputable VPN before connecting to Tor adds an extra layer of security by masking your internet activity from your Internet Service Provider (ISP).
- Updated Security Software: Ensure your operating system and antivirus are up-to-date. The dark web can host malicious software.
- Discipline: Never use personal information, real names, or passwords. Do not download files unless absolutely necessary and from a trusted source.
What You Will Find: Beyond the Myths
The dark web's reputation is often tied to illegal marketplaces, but it serves other vital purposes. It is a double-edged sword.
- Whistleblowing and Journalism: Platforms like SecureDrop allow sources to leak information to news organizations anonymously, protecting them from retaliation.
- Privacy for Activists: In oppressive regimes, dissidents use it to communicate and organize without government surveillance.
- Illicit Marketplaces: Unfortunately, these exist, selling everything from stolen data to contraband. This is the dangerous and illegal side.
- Legal Forums and Libraries: There are communities discussing privacy, technology, and hosting archives of books or information that may be censored elsewhere.
Critical Safety and Legal Warnings
Navigating this space carries significant risks. Ignorance is not a legal defense.
- Legality: Simply accessing the dark web is legal in most countries. However, engaging in illegal activities is a crime. Law enforcement monitors these spaces.
- Scams are Rampant: Trust is a vulnerability. Many sites exist to steal cryptocurrency or infect your device.
- Psychological Harm: You may stumble upon disturbing, illegal, or explicit content. Extreme caution is advised.
- Digital Footprint: While anonymous, poor practices (like enabling browser plugins or opening documents) can reveal your identity.
- The dark web is part of the hidden web, which comprises non-indexed websites that are mostly used for illegal and illicit activity.
- Excavator is perhaps as controversial as it gets, among the most comprehensive search engines on the dark network.
- The Tor Browser can take you to all kinds of questionable, dangerous, and potentially illegal content.
- No, the dark web isn’t illegal, but what you do while in the underbelly of the internet matters.
- Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable.
- Finding content on the dark web isn’t as straightforward as using Google.
FAQs About Accessing the Dark Web
Is it illegal to browse the dark web?
No, in most jurisdictions, the act of browsing is not illegal. It becomes illegal when you participate in or purchase illegal goods and services.
Can I be tracked on the dark web?
The Tor network is designed to prevent tracking. However, sophisticated techniques, user error, or malware can potentially compromise your anonymity.
Do I need to be a tech expert?
No. Downloading and using the Tor Browser is straightforward. The required expertise lies in practicing relentless operational security.
Why would a regular person need to know this?
Understanding the infrastructure demystifies it, promotes informed discussions on privacy laws, and highlights the importance of protecting one's own data on the surface web.
Ultimately, learning how to acess the dark web is about education, not participation. It reveals the complexities of online privacy, the tools used to protect it, and the stark realities of unregulated digital space. This knowledge is power—the power to advocate for a safer internet and to protect yourself within it.



