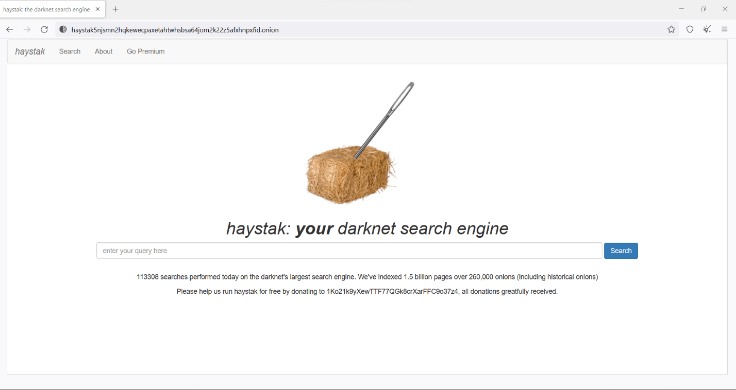
The .onion domain suffix represents a hidden service network operating within the Tor anonymity system. These sites are not indexed by conventional search engines and require the Tor browser to access, routing traffic through encrypted layers to conceal the location of both the user and the server. This architecture provides strong anonymity, making it a critical tool for whistleblowers and dissidents operating under oppressive regimes.
This same layer of privacy also fosters clandestine markets and communities that trade in illegal goods, stolen data, and prohibited content. The .onion ecosystem exists as a dual-edged digital frontier, embodying both the ultimate expression of untraceable free speech and a largely ungoverned space where criminal enterprises can operate with significant insulation from conventional law enforcement tactics.
In October 2014, The Tor Project hired the public relations firm Thomson Communications to improve its public image (particularly regarding the terms "Dark Net" and "hidden services," which are widely viewed as being problematic) and to educate journalists about the technical aspects of Tor. Tor executive director Andrew Lewman said that even though it accepts funds from the U.S. federal government, the Tor service did not collaborate with the NSA to reveal identities of users. Tor has been praised for providing privacy and anonymity to vulnerable Internet users such as political activists fearing surveillance and arrest, ordinary web users seeking to circumvent censorship, and people who have been threatened with violence or abuse by stalkers. To allow download from places where accessing the Tor Project URL may be risky or blocked, a GitHub repository is maintained with links for releases hosted in other domains. Like client applications that use Tor, servers relying on onion services for protection can introduce their own weaknesses.
The internet is a vast landscape, but much like an iceberg, the majority of its content lies beneath the surface. Beyond the familiar websites indexed by search engines exists a deeper layer, often shrouded in mystery and misconception. This article aims to demystify one of its most well-known aspects: the .onion dark web.
What is the .onion Dark Web?
The .onion dark web refers to a collection of websites that are not accessible through standard browsers like Chrome or Firefox. These sites use a special .onion domain suffix and require specific software, primarily The Onion Router (Tor) network, to visit. The core principle is enhanced privacy and anonymity for both visitors and site operators.
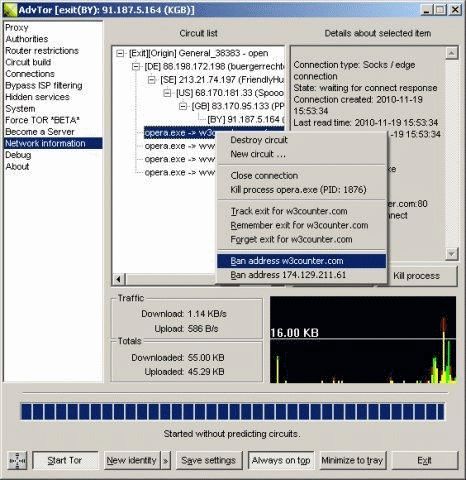
How Does the .onion Network Work?
Instead of connecting directly to a website, your connection through the Tor browser is routed through a series of volunteer-operated servers called relays. This process, known as onion routing, encrypts your data multiple times and peels away each layer at a different relay, obscuring the origin and destination of the traffic. This makes it extremely difficult to track a user's activity or pinpoint a website's physical server location.
Common Uses of .onion Sites
While often associated with illegal marketplaces, the dark web serves a wide range of legitimate purposes where anonymity is crucial:
- Tails routes traffic through Tor and forgets state by default when shut down.
- There are many scam .onion sites also present which end up giving tools for download that are infected with trojan horses or backdoors.
- Others may act in ways that are illegal for the protection and safety of others.
- Attacks from malicious exit relays have recorded usernames and passwords, and modified Bitcoin addresses to redirect transactions.
- Dual access through clearnet and onion interfaces
- Privacy-Conscious Communication: Used by journalists, activists, and whistleblowers in repressive regimes to communicate and share information safely.
- Bypassing Censorship: Providing access to news and information in countries with heavy internet restrictions.
- Secure Forums: Hosting support groups for sensitive topics where users fear stigma or retaliation.
- Research and Journalism: Allowing investigators and reporters to explore and document all facets of the internet.
Important Risks and Considerations
Navigating the .onion dark web carries significant risks that must be understood:
- Illegal Content: It hosts markets for illicit goods, hacking services, and other illegal activities. Accessing such material is a crime.
- Scams and Malware: The lack of regulation makes scams, fraud, and malware-distributing sites prevalent.
- Law Enforcement Monitoring: Contrary to popular belief, anonymity is not absolute. Law enforcement agencies operate on these networks.
- Psychological Harm: Users may accidentally encounter disturbing or harmful content.
Frequently Asked Questions (FAQs)
Is using Tor or visiting .onion sites illegal?
No. Using the Tor browser or accessing .onion sites for legitimate purposes is legal in most countries. The tool itself is a project focused on privacy and free speech. However, illegal activities conducted on it remain illegal.
Can I be tracked on the dark web?
While Tor provides strong anonymity, it is not foolproof. User errors, such as downloading files or enabling browser plugins, can compromise privacy. Advanced techniques by determined adversaries can also potentially de-anonymize users.
Should I explore the dark web out of curiosity?
It is generally not advised. The risks of encountering illegal content, malware, or scams are high. The information needed for educational purposes can be sufficiently obtained through research and articles about the .onion dark web without direct access.
How can I stay safe if I need to use it?
If you have a legitimate need, essential safety steps include: using the official Tor Browser, never disabling its security settings, avoiding downloading files, not sharing personal information, and using a VPN in conjunction with Tor only if you understand the potential trade-offs in security.
- For the purpose of this article, “dark web site” will specifically reference services on the Tor network.
- The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.
- Fifteen years have passed since a couple of MIT grads and a Navy-funded researcher first built The Onion Router, or Tor, a wild experiment in granting anonymity to anyone online.
- So, you should still use strong passwords and two-factor authentication (2FA) to protect your accounts even when using Proton Mail on Tor.
- Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies.
Understanding the .onion dark web is about separating fact from fiction. It is a technological reality that underscores the dual-use nature of tools designed for privacy. Being informed about its mechanics, legitimate uses, and inherent dangers is crucial for navigating the modern digital world responsibly and safely.